Configure Encryption (RPM/DEB)
In addition to the transport-level encryption that is always in effect between your cluster and Pepperdata, and the secure https access that the Pepperdata dashboard requires, you can enable 128-bit AES-CBC (symmetric) storage-level encryption for sensitive data at rest, such as user names, hostnames, and job and queue names.
When this extra level of encryption is enabled, Pepperdata receives and stores only the encrypted version.
To configure encryption for your cluster, add the PD_ENCRYPTION_KEY and PD_ANONYMIZE variables to your Pepperdata configuration file, /etc/pepperdata/pepperdata-config.sh.
Notes and Limitations
-
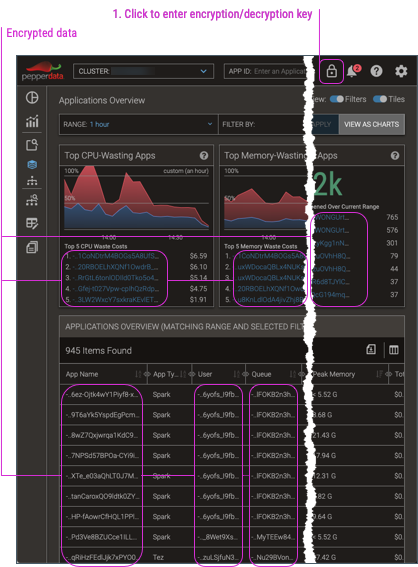
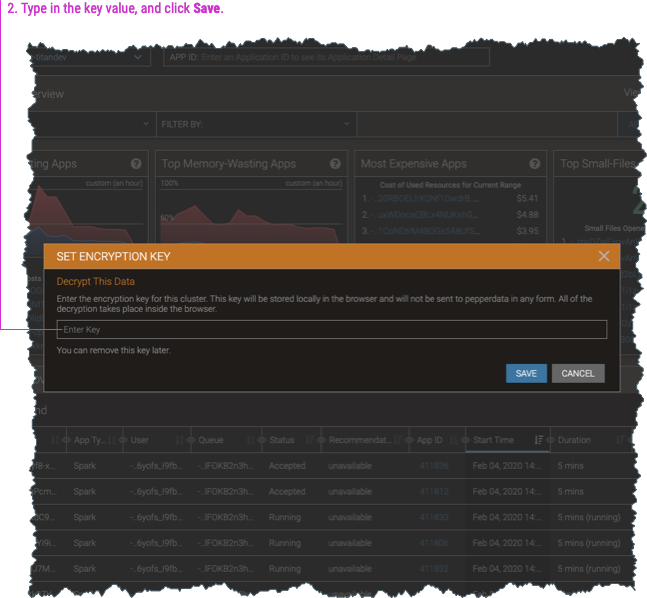
When you enable encryption, the dashboard by default shows the data in its encrypted form. To view the decrypted data, you must enter the encryption key (which is also used to decrypt the data) into any dashboard page.
-
Impala data cannot be encrypted.
-
Although you can perform full-text searches for application names even with encryption, partial matches are unsupported. For example, if the application name is “hive”, searching for “hive” yields the expected result. But when encryption is applied to perform the search, the encrypted value for a partial search string will not match any portion of the encrypted value of the full string. Therefore “hiv” cannot be matched if the full name of the application is “hive”.
-
If you use the Pepperdata REST API to access data from encrypted clusters, you’ll need to decrypt the returned data strings; see Decrypt Data Returned for Encrypted Clusters.
Procedure
-
Generate an encryption key, which is also used to decrypt the data for your Pepperdata dashboard display.
-
You can use a commercial or open source tool to create a randomly-generated key; for example, the OpenSSL command,
openssl rand -hex 16. -
You can manually create any arbitrary string to use as your key; for example,
MyCustomEncryptionKey. -
Be sure to keep your key secret and secure in accordance with your organization’s security policies.
-
-
On any host in the cluster, open the Pepperdata configuration file,
/etc/pepperdata/pepperdata-config.sh, for editing. -
Add the following variables. Be sure to replace the
my-encrypt-decrypt-keyplaceholder with your actual encryption key.export PD_ENCRYPTION_KEY=my-encrypt-decrypt-key export PD_ANONYMIZE=1 -
Save your changes and close the file.
-
On every host in the cluster, restart the Pepperdata services.
-
Restart the Pepperdata Collector.
You can use either the
service(if provided by your OS) orsystemctlcommand:sudo service pepcollectd restartsudo systemctl restart pepcollectd
-
Restart the PepAgent.
You can use either the
service(if provided by your OS) orsystemctlcommand:sudo service pepagentd restartsudo systemctl restart pepagentd
-
